1/14
Some thoughts on
AEZ
- v. 4
Viet Tung Hoang Florida State University USA Phillip Rogaway Univ of California, Davis USA Ted Krovetz Sacramento State USA DIAC 2016 Nagoya, Japan
27 September 2016
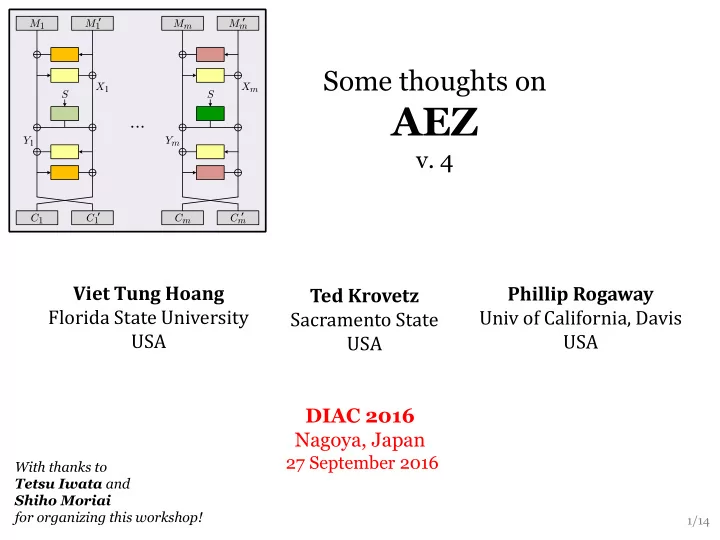
M1 M1 C1 C1 X1 Mm Mm Cm Cm Xm Y1 S S ’ ’ ’ ’ Ym
...
With thanks to Tetsu Iwata and Shiho Moriai for organizing this workshop!