Page1
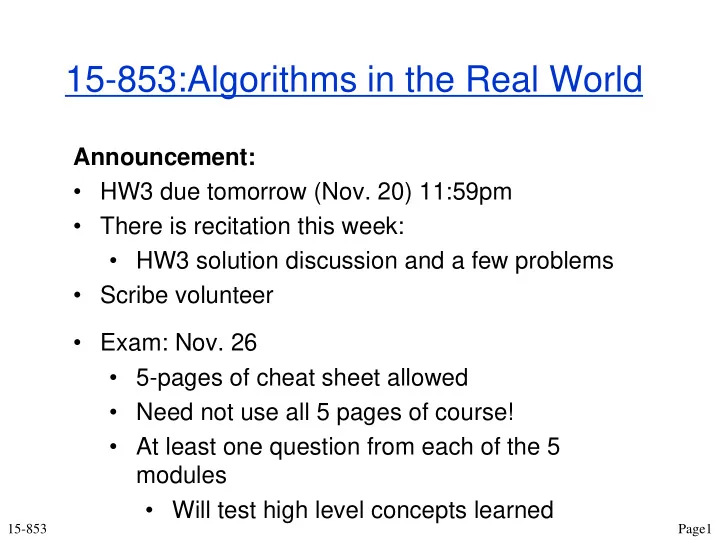
15-853:Algorithms in the Real World
15-853
Announcement:
- HW3 due tomorrow (Nov. 20) 11:59pm
- There is recitation this week:
- HW3 solution discussion and a few problems
- Scribe volunteer
- Exam: Nov. 26
- 5-pages of cheat sheet allowed
- Need not use all 5 pages of course!
- At least one question from each of the 5
modules
- Will test high level concepts learned