1
1 Cryptographic Elections: Challenges and Opportunities Alon Rosen - - PowerPoint PPT Presentation
1 Cryptographic Elections: Challenges and Opportunities Alon Rosen - - PowerPoint PPT Presentation
1 Cryptographic Elections: Challenges and Opportunities Alon Rosen IDC Herzliya June 9, 2010 2 Thanks Ben Adida (Harvard University) Yuval Kedem (Gallileo) David Movshovitz (IDC Herzlyia) Shimon Schocken (IDC Herzlyia)
Cryptographic Elections: Challenges and Opportunities
Alon Rosen IDC Herzliya June 9, 2010
2
Thanks
- Ben Adida (Harvard University)
- Yuval Kedem (Gallileo)
- David Movshovitz (IDC Herzlyia)
- Shimon Schocken (IDC Herzlyia)
- Amnon Ta-Shma (T
el Aviv University)
3
This Talk
Part I
➡ Electronic voting in US ➡ The Israeli perspective
Part II
➡ Why is voting so hard? ➡ Cryptographic voting.
4
http://www.nytimes.com/2008/01/06/magazine/06Vote-t.html 5
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
Voting in the US
http://www.cs.uiowa.edu/~jones/voting/pictures/ 6
7
- HAVA - Help America
Vote Act
- 4 Billion dollars allocated
- Mostly to replace voting machines
7
- HAVA - Help America
Vote Act
- 4 Billion dollars allocated
- Mostly to replace voting machines
7
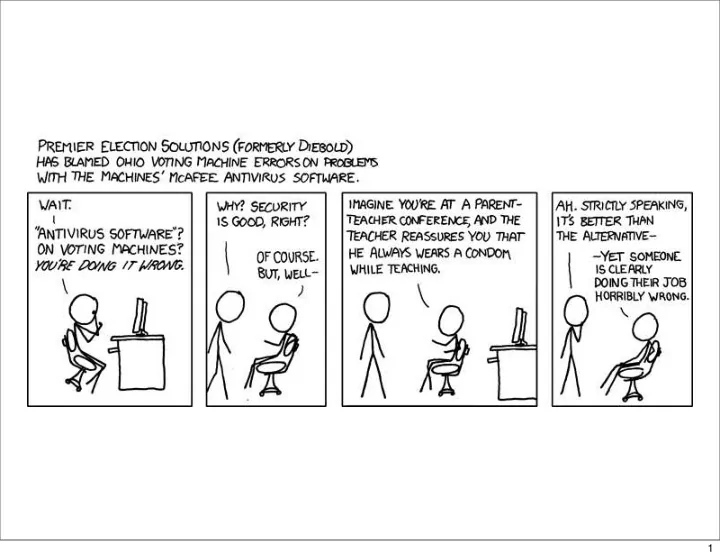
The Princeton Report
- Diebold touch-screen runs
executable code loaded from memory card
- All audit logs modified
to be consistent
- Can spread virally by
memory card.
[FHF2006]
8
- New Mexico (March 2006)
- California (August 2007)
- Florida (December 2007)
- Ohio (January 2008)
- Iowa (March 2008)
- ...
- States that mandate paper trail.
9
10
Debra Bowen
10
- Simple and reliable system
- Voter secrecy
- Quick count
- And in addition: transparency (open audit).
What does Everbody Want?
11
What is Transparency?
Anyone can verify that:
- their vote was cast as intended
- the votes were count as cast
12
Paper vs. Electronic
Electronic elections today:
- Global attacks
- Undetectable
- Unrecoverable
- No transparency
Paper elections:
- Local attacks
- No transparency
13
Paper vs. Electronic
Electronic elections today:
- Global attacks
- Undetectable
- Unrecoverable
- No transparency
Paper elections:
- Local attacks
- No transparency
Ideally:
- No local/global attacks
- Full transparency
13
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg 14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg 14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
- Failures are obvious
14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
- Failures are obvious
14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
- Failures are obvious
- Complete audit logs
14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
- Failures are obvious
- Complete audit logs
- Transferability of claims
14
Aviation and Banking?
http://www.sxc.hu/photo/206579 http://commons.wikimedia.org/wiki/Image:738100.jpg
- Little defense against insiders
- Failures are obvious
- Complete audit logs
- Transferability of claims
These are poor analogies.
14
Open-Source?
15
Software Independence [Rivest, Wack’06]
“A voting system is software independent if an undetected change or error in its software cannot cause an undetectable change or error in an election outcome”
16
Examples
http://www.youtube.com/watch?v=zeHmsrLc4jc 17
Examples
http://www.youtube.com/watch?v=zeHmsrLc4jc 17
Non-example
18
The Israeli Perspective
- Nov ’07: Pilot of electronic voting with
touch screens in several municipalities.
- Nov ’07: Minister of interior announces plan
to move to electronic elections
- Apr ’08: TEHILA are given mandate to run
pilot in 3 municipalities.
- Sep’08 - today: Legislation underway to
accommodate pilot.
19
The process:
- No public scrutiny
- No open design
The result:
- No paper trail
- No software independence
20
Why is Voting so Hard?
21
The Point of An Election
“The People have spoken.... the bastards!”
Dick Tuck 1966 Concession Speech
22
The Point of An Election
“The People have spoken.... the bastards!”
Dick Tuck 1966 Concession Speech
Provide enough evidence to convince the loser.
22
http://www.cs.uiowa.edu/~jones/voting/pictures/ 23
Secret Ballot vs. Verifiability
24
Secret Ballot vs. Verifiability
Voting System
24
Secret Ballot vs. Verifiability
Voting System Alice convince
24
Secret Ballot vs. Verifiability
Voting System Alice convince
Carl the Coercer
24
Secret Ballot vs. Verifiability
Voting System Alice convince
Carl the Coercer
24
Desired Properties
(1)Alice verifies her vote. (2)Everyone verifies tallying. (3)Alice cannot be coerced by Eve.
25
http://www.cs.uiowa.edu/~jones/voting/pictures/
1892 - Australian Ballot
26
The Ballot Handoff
Alice the Voter
Sweet
27
The Ballot Handoff
Alice the Voter
Sweet
27
The Ballot Handoff
Alice the Voter
Sweet
27
The Ballot Handoff
Alice the Voter
Sweet
27
Salty Sweet Salty Sweet Sweet
The Ballot Handoff
Alice the Voter
Sweet
27
Salty Sweet Salty Sweet Sweet
The Ballot Handoff
Alice the Voter
Sweet
Black Box
27
Chain of Custody
28
Chain of Custody
Vendor
/* * source * code */ if (...
1
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 4
Alice
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 4
Alice
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 Ballot Box Collection 5 4
Alice
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 Ballot Box Collection 5 Results ..... 6 4
Alice
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 Ballot Box Collection 5 Results ..... 6 4
Alice
This is where paper trail helps
28
Chain of Custody
Voting Machine 2
Vendor
/* * source * code */ if (...
1 Polling Location 3 Ballot Box Collection 5 Results ..... 6 4
Alice
This is where paper trail helps Black box (even with paper trail)
28
Threat Model
29
Threat Model
Who is the attacker?
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit?
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit?
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
➡ corruption of input, ballot box, transport, tallying
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
➡ corruption of input, ballot box, transport, tallying ➡ coercion of voters
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
➡ corruption of input, ballot box, transport, tallying ➡ coercion of voters
Where will the attacks be hidden?
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
➡ corruption of input, ballot box, transport, tallying ➡ coercion of voters
Where will the attacks be hidden?
➡ honest mistakes: randomly distributed in the process
29
Threat Model
Who is the attacker?
➡ administration officials, candidates, poll workers, even voters
What is the Benefit? How will the attacks be carried out?
➡ corruption of input, ballot box, transport, tallying ➡ coercion of voters
Where will the attacks be hidden?
➡ honest mistakes: randomly distributed in the process ➡ malicious intent: hiding where you least defend
29
So what can we do?
30
Wooten got the news from his wife, Roxanne, who went to City Hall on Wednesday to see the election results. “She saw my name with zero votes by it. She came home and asked me if I had voted for myself or not. I told her I did,” said Wooten, owner of local bar.
31
Open audit elections
Cryptography provides more than confidentiality. Cryptography can provide both verifiability and ballot secrecy Anyone can audit!
32
Bulletin Board
Public Ballots
Bridget: Sweet Carol: Salty
33
Bulletin Board
Public Ballots
Bridget: Sweet Carol: Salty
Alice
33
Bulletin Board
Public Ballots
Alice: Sweet Bridget: Sweet Carol: Salty
Alice
33
Bulletin Board
Public Ballots
Alice: Sweet Bridget: Sweet Carol: Salty
Tally Sweet.......2 Salty..........1
Alice
33
Encrypted Public Ballots
Bulletin Board
Alice: Rice Bridget: Clinton Carol: Rice
Tally Sweet.......2 Salty..........1
Alice
34
Encrypted Public Ballots
Bulletin Board
Alice: Rice Bridget: Clinton Carol: Rice
Tally Sweet.......2 Salty..........1
Alice
Alice verifies her vote
34
Encrypted Public Ballots
Bulletin Board
Alice: Rice Bridget: Clinton Carol: Rice
Tally Sweet.......2 Salty..........1
Alice
Alice verifies her vote Everyone verifies the tally
34
Public-Key Encryption
35
Public-Key Encryption
Keypair consists of a public key and a secret key .
sk pk
35
Public-Key Encryption
Keypair consists of a public key and a secret key .
sk pk
"Salty" 8b5637
Encpk
35
Public-Key Encryption
Keypair consists of a public key and a secret key .
sk pk
"Salty" 8b5637
Encpk
c5de34
Encpk
"Sweet"
35
Public-Key Encryption
Keypair consists of a public key and a secret key .
sk pk
"Salty" 8b5637
Encpk
c5de34
Encpk
"Sweet" a4b395
Encpk
"Salty"
35
Threshold Decryption
8b5637
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Threshold Decryption
8b5637 b739cb
Decsk1
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Threshold Decryption
8b5637 b739cb
Decsk1
261ad7
Decsk2
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Threshold Decryption
8b5637 b739cb
Decsk1
261ad7
Decsk2
7231bc
Decsk3
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Threshold Decryption
8b5637 b739cb
Decsk1
261ad7
Decsk2
7231bc
Decsk3
8239ba
Decsk4
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Threshold Decryption
8b5637 b739cb
Decsk1
261ad7
Decsk2
7231bc
Decsk3
8239ba
Decsk4
"Salty"
Secret key is shared amongst multiple parties: all (or at least a quorum) need to cooperate to decrypt.
36
Tallying Method I: Homomorphic Tabulation [Benaloh’87]
Enc(m1) × Enc(m2) = Enc(m1 + m2)
37
Tallying Method I: Homomorphic Tabulation [Benaloh’87]
Yes = Enc(1) No = Enc(0) Enc(m1) × Enc(m2) = Enc(m1 + m2)
37
Tallying Method I: Homomorphic Tabulation [Benaloh’87]
Yes = Enc(1) No = Enc(0)
Bulletin Board
Alice:
Bridget:
Carol:
Enc(ma) Enc(mb) Enc(mc)
Enc(m1) × Enc(m2) = Enc(m1 + m2)
37
Tallying Method I: Homomorphic Tabulation [Benaloh’87]
Yes = Enc(1) No = Enc(0)
Bulletin Board
Alice:
Bridget:
Carol:
Enc(ma) Enc(mb) Enc(mc)
EncryptedTally = Enc(ma) × Enc(mb) × Enc(mc) = Enc(ma + mb + mc) Enc(m1) × Enc(m2) = Enc(m1 + m2)
37
Tallying Method II: Mixnet [Chaum‘81]
Labor Likkud Supreme court
38
Tallying Method II: Mixnet [Chaum‘81]
Labor Likkud Supreme court
Each mix server shuffles the encrypted votes.
38
How can we verify
- perations on
encrypted data?
39
Verifying Validity of Encryption/Mixing
Given Enc(m) How can I verify:
- 1. that it is not an encryption of more than one vote?
- 2. that the encryption of my vote wasn’t “dropped”?
Zero-Knowledge proofs: Can prove validity of Enc(m) without revealing anything else! The crucial point: only need to verify that machine is computing right functionality...
40
Verifying Validity of Encryption/Mixing
Given Enc(m) How can I verify:
- 1. that it is not an encryption of more than one vote?
- 2. that the encryption of my vote wasn’t “dropped”?
Zero-Knowledge proofs: Can prove validity of Enc(m) without revealing anything else! The crucial point: only need to verify that machine is computing right functionality...
40
Voting Process Example
[Chaum’81, Sako-Kilian’95, Neff’04, Chaum’04, etc...]
41
Alice
Identification
2
Polling station committee
42
Alice
Identification
2
ID Polling station committee
42
Alice
Identification
2
ID Ballot(s) Polling station committee
42
The Ballot
Fold Tear
43
Alice
+ Producing Encrypted Ballot
44
Alice
+ Producing Encrypted Ballot
44
Alice
+ Producing Encrypted Ballot
44
Alice
+ Producing Encrypted Ballot
Sweet
44
Encrypted Ballot
Sweet Sweet
45
Ballot Casting
1
46
Ballot Casting
1 2
46
Ballot Casting
4
Alice
3 1 2
46
Ballot Casting
4
Alice
3 1 2
Receipt
4
46
Verifying Consistency [Benaloh]
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
Verifying Consistency [Benaloh]
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot
Alice "CAST"
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot
Alice "CAST"
Signed Encrypted Ballot http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot
Alice "CAST"
Signed Encrypted Ballot
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Decrypted Ballot Encrypted Ballot VERIFICATION 47
"AUDIT"
Verifying Consistency [Benaloh]
Alice "Vote for Sweet"
Encrypted Ballot
Alice
Decrypted Ballot
Alice "CAST"
Signed Encrypted Ballot
Alice
http://en.wikipedia.org/wiki/Image:Barcode-scanner.jpg Signed Encrypted Ballot Decrypted Ballot Encrypted Ballot VERIFICATION 47
The Tallying Process
- Paper tally
- Electronic tally
- 1. Homomorphic public-key encryption or mixnets
- 2. Zero-knowledge proofs
48
Putting It Together
Voting Equipment & Ballot Flow Verification 49
Putting It Together
Voting Equipment & Ballot Flow Verification
Polling Location Voting Machine
Vendor
/* * source * code */ if (... 49
Putting It Together
Voting Equipment & Ballot Flow Verification
Polling Location Voting Machine
Vendor
/* * source * code */ if (...
Public Ballot Box
Alice
49
Putting It Together
Voting Equipment & Ballot Flow Verification
Polling Location Voting Machine
Vendor
/* * source * code */ if (...
Results ..... Public Ballot Box
Alice
49
Putting It Together
Voting Equipment & Ballot Flow Verification
Polling Location Voting Machine
Vendor
/* * source * code */ if (...
Receipt 1 Results ..... Public Ballot Box
Alice
49
Putting It Together
Voting Equipment & Ballot Flow Verification
Polling Location Voting Machine
Vendor
/* * source * code */ if (...
Receipt 1 2 Results ..... Public Ballot Box
Alice
49
Open-Audit Elections
- Alice verifies her vote.
- Everyone verifies the tally.
- Incoercibility is enforced.
50
Open-Audit Elections
- Alice verifies her vote.
- Everyone verifies the tally.
- Incoercibility is enforced.
Anyone can Audit.
50
Open Audit Voting:Helios (Ben Adida, 2009)
51
Open Audit Voting: Scantegrity II (Chaum et al., 2009)
52
Questions?
53