SLIDE 1 1
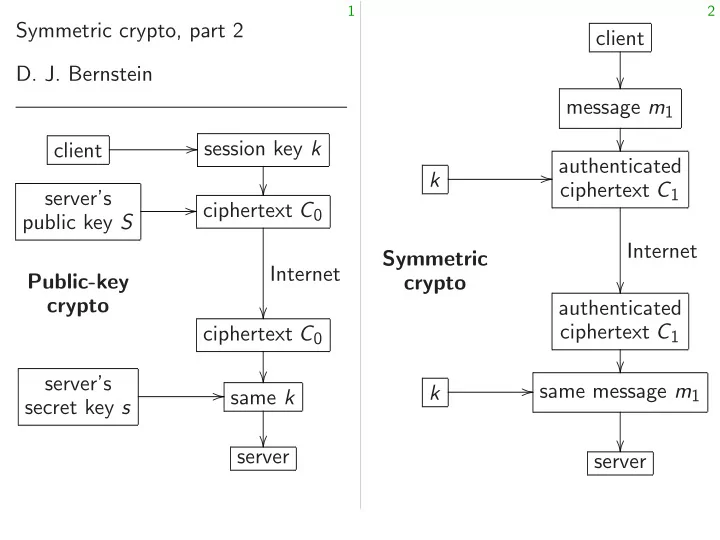
Symmetric crypto, part 2
client session key k
public key S ciphertext C0 Internet
crypto ciphertext C0
secret key s same k
2
client
authenticated ciphertext C1 Internet
crypto authenticated ciphertext C1
same message m1

SLIDE 2 1
Symmetric crypto, part 2
client session key k
public key S ciphertext C0 Internet
crypto ciphertext C0
secret key s same k
2
client
authenticated ciphertext C2 Internet
crypto authenticated ciphertext C2
same message m2

SLIDE 3 1
Symmetric crypto, part 2
client session key k
public key S ciphertext C0 Internet
crypto ciphertext C0
secret key s same k
2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”

SLIDE 4 1
Symmetric crypto, part 2 Bernstein client session key k
key S ciphertext C0 Internet
crypto ciphertext C0
secret key s same k
2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
Symmetric Integrity: Attacker

SLIDE 5 1
ypto, part 2 session key k
Internet
- ciphertext C0
- same k
- server
2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
Symmetric crypto: Integrity: Attacker can’t forge

SLIDE 6 1
session key k
Internet
- ciphertext C0
- same k
- server
2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts.

SLIDE 7 2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts.

SLIDE 8 2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.)

SLIDE 9 2
client
authenticated ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
“forgery!”
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability.

SLIDE 10 2
client
ciphertext C3 Internet
crypto forged ciphertext C′
3 = C3
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability. Easy encryption Assume Assume secret 30- t1 to use t2 to use t3 to use

SLIDE 11 2
client
ciphertext C3 Internet
ciphertext C′
3 = C3
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability. Easy encryption mechanism: Assume 30-digit messages. Assume client, server secret 30-digit numb t1 to use for message t2 to use for message t3 to use for message

SLIDE 12 2
client
ciphertext C3 Internet
ciphertext C′
3 = C3
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability. Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc.

SLIDE 13
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability.
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc.

SLIDE 14
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability.
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality.

SLIDE 15
3
Symmetric crypto: main objectives Integrity: Attacker can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) Can define further objectives. Example: If crypto is too slow, attacker can flood server’s CPU. Real client messages are lost. This damages availability.
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030.

SLIDE 16
3
Symmetric crypto: main objectives Integrity: er can’t forge ciphertexts. Confidentiality: Attacker seeing ciphertexts can’t figure out message contents. (But can see message number, length, timing.) define further objectives. Example: If crypto is too slow, er can flood server’s CPU. client messages are lost. damages availability.
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030. Last time: compute using another Sender attaches to messa Receiver This prote

SLIDE 17 3
ypto: main objectives forge ciphertexts. y: Attacker seeing figure out
er, length, timing.) er objectives. crypto is too slow, d server’s CPU. messages are lost. availability.
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030. Last time: For each compute authenticato using another secret Sender attaches authenticato to message before Receiver checks authenticato This protects integrit

SLIDE 18 3
ciphertexts. seeing
can see timing.)
slow, CPU. lost. .
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030. Last time: For each message compute authenticator using another secret number. Sender attaches authenticato to message before sending it. Receiver checks authenticato This protects integrity.

SLIDE 19
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030.
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity.

SLIDE 20
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030.
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up.

SLIDE 21
4
Easy encryption mechanism: Assume 30-digit messages. Assume client, server know secret 30-digit numbers t1 to use for message 1; t2 to use for message 2; t3 to use for message 3; etc. C1 = (m1 + t1) mod 1030; C2 = (m2 + t2) mod 1030; C3 = (m3 + t3) mod 1030; etc. This protects confidentiality. AES-GCM, ChaCha20-Poly1305 work this way, scaled up to groups larger than Z=1030.
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers.

SLIDE 22
4
encryption mechanism: Assume 30-digit messages. Assume client, server know 30-digit numbers use for message 1; use for message 2; use for message 3; etc. m1 + t1) mod 1030; m2 + t2) mod 1030; m3 + t3) mod 1030; etc. rotects confidentiality. AES-GCM, ChaCha20-Poly1305 this way, scaled up to larger than Z=1030.
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers. AES expands into F(k simulating secrets r

SLIDE 23
4
mechanism: messages. server know numbers message 1; message 2; message 3; etc. mod 1030; mod 1030; mod 1030; etc. confidentiality. ChaCha20-Poly1305 caled up to than Z=1030.
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers. AES expands 256-bit into F(k; 1); F(k; 2) simulating many indep secrets r; s1; t1; : : :

SLIDE 24 4
mechanism: messages. etc. etc. confidentiality.
to .
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers. AES expands 256-bit secret into F(k; 1); F(k; 2); F(k; 3) simulating many independent secrets r; s1; t1; : : :.

SLIDE 25
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :.

SLIDE 26
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F.

SLIDE 27
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks.

SLIDE 28
5
Last time: For each message compute authenticator using another secret number. Sender attaches authenticator to message before sending it. Receiver checks authenticator. This protects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 work this way, again scaled up. This would be the whole picture if client, server started with enough secret random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings.

SLIDE 29 5
time: For each message compute authenticator another secret number. Sender attaches authenticator message before sending it. Receiver checks authenticator. rotects integrity. Details use multiplications. AES-GCM, ChaCha20-Poly1305 this way, again scaled up.
client, server started with enough secret random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings. PRF (“pseudo Attacker F(k; 1); F independent blocks, given that returns Server is

SLIDE 30
5
each message authenticator secret number. authenticator re sending it. authenticator. integrity. multiplications. ChaCha20-Poly1305 again scaled up. the whole picture started with random numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings. PRF (“pseudorandom Attacker can’t distinguish F(k; 1); F(k; 2); F( independent uniform blocks, given access that returns F(k; i Server is called an

SLIDE 31 5
essage er. authenticator it. authenticator. multiplications.
scaled up. picture with numbers.
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings. PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle.

SLIDE 32
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings.
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle.

SLIDE 33
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings.
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle.

SLIDE 34
6
AES expands 256-bit secret k into F(k; 1); F(k; 2); F(k; 3); : : : simulating many independent secrets r; s1; t1; : : :. ChaCha20 also does this, using a different function F. Definition of PRG (“pseudorandom generator”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from string of independent uniform random blocks. Warning: “pseudorandom” has many other meanings.
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG.

SLIDE 35
6
expands 256-bit secret k (k; 1); F(k; 2); F(k; 3); : : : simulating many independent r; s1; t1; : : :. ChaCha20 also does this, a different function F. Definition of PRG (“pseudorandom generator”): er can’t distinguish 1); F(k; 2); F(k; 3); : : : string of independent random blocks. rning: “pseudorandom” many other meanings.
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG. Small blo PRF prop application

SLIDE 36
6
256-bit secret k ; 2); F(k; 3); : : : independent : :. does this, function F. PRG generator”): distinguish F(k; 3); : : : independent blocks. “pseudorandom” meanings.
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG. Small block sizes a PRF property fails, application security

SLIDE 37
6
secret k 3); : : : endent F. r”): : : endent random”
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG. Small block sizes are dangerous. PRF property fails, and often application security fails.

SLIDE 38
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails.

SLIDE 39
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck.

SLIDE 40
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q?

SLIDE 41
7
PRF (“pseudorandom function”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random blocks, given access to a server that returns F(k; i) given i. Server is called an oracle. PRP (“: : : permutation”): Attacker can’t distinguish F(k; 1); F(k; 2); F(k; 3); : : : from independent uniform random distinct blocks, given oracle. If block size is big then PRP ⇒ PRF ⇒ PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits.

SLIDE 42
7
(“pseudorandom function”): er can’t distinguish 1); F(k; 2); F(k; 3); : : : from endent uniform random cks, given access to a server returns F(k; i) given i. is called an oracle. (“: : : permutation”): er can’t distinguish 1); F(k; 2); F(k; 3); : : : independent uniform random distinct blocks, given oracle. ck size is big then PRF ⇒ PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits. Can prove integrity ChaCha20-P AES and

SLIDE 43
7
random function”): distinguish F(k; 3); : : : from uniform random access to a server ; i) given i. an oracle. ermutation”): distinguish F(k; 3); : : : endent uniform random given oracle. big then PRG.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits. Can prove confidentialit integrity of AES-GCM ChaCha20-Poly1305 AES and ChaCha20

SLIDE 44
7
function”): : : from random erver i. ermutation”): : : random racle.
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits. Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs.

SLIDE 45
8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs.

SLIDE 46 8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.

SLIDE 47 8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more.

SLIDE 48 8
Small block sizes are dangerous. PRF property fails, and often application security fails. e.g. 2016 Bhargavan–Leurent sweet32.info: Triple-DES broken in TLS. Same attack also breaks small block sizes in NSA’s Simon, Speck. AES block size: 128 bits. PRF attack chance ≈ q2=2129 if AES is used for q blocks. Is this safe? How big is q? ChaCha20 block size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully!

SLIDE 49 8
block sizes are dangerous. roperty fails, and often application security fails. 2016 Bhargavan–Leurent sweet32.info: Triple-DES in TLS. Same attack eaks small block sizes NSA’s Simon, Speck. block size: 128 bits. attack chance ≈ q2=2129 is used for q blocks. safe? How big is q? ChaCha20 block size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully! How do ChaCha20

SLIDE 50 8
sizes are dangerous. fails, and often security fails. rgavan–Leurent Triple-DES Same attack small block sizes Simon, Speck. 128 bits. chance ≈ q2=2129 r q blocks. w big is q? size: 512 bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully! How do we know that ChaCha20 are PRFs?

SLIDE 51 8
dangerous.
rgavan–Leurent
attack sizes 2129 cks. bits.
9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully! How do we know that AES an ChaCha20 are PRFs? We don’t.

SLIDE 52 9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t.

SLIDE 53 9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.”

SLIDE 54 9
Can prove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming AES and ChaCha20 are PRFs. Generalization: Prove security
- f M(F) assuming cipher F is a
- PRF. M is a mode of use of F.
Good modes: CTR (“counter mode”), CBC, OFB, many more. Bad modes: ECB, many more. Mode that claimed proof but was recently broken: OCB2. Have to check proofs carefully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.” Remaining slides today:
- Simple example of block cipher.
Seems to be a good cipher, except block size is too small.
- Variants of this block cipher
that look similar but can be quickly broken.

SLIDE 55 9
rove confidentiality and integrity of AES-GCM and ChaCha20-Poly1305 assuming and ChaCha20 are PRFs. Generalization: Prove security F) assuming cipher F is a M is a mode of use of F. modes: CTR (“counter de”), CBC, OFB, many more. modes: ECB, many more. that claimed proof as recently broken: OCB2. to check proofs carefully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.” Remaining slides today:
- Simple example of block cipher.
Seems to be a good cipher, except block size is too small.
- Variants of this block cipher
that look similar but can be quickly broken. 1994 Wheeler–Needham a tiny encryption
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 56 9
confidentiality and AES-GCM and
ChaCha20 are PRFs. Prove security assuming cipher F is a de of use of F. CTR (“counter OFB, many more. ECB, many more. claimed proof broken: OCB2. roofs carefully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.” Remaining slides today:
- Simple example of block cipher.
Seems to be a good cipher, except block size is too small.
- Variants of this block cipher
that look similar but can be quickly broken. 1994 Wheeler–Needham a tiny encryption algo
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 57 9
and assuming PRFs. security F is a
(“counter more. more. OCB2. refully!
10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.” Remaining slides today:
- Simple example of block cipher.
Seems to be a good cipher, except block size is too small.
- Variants of this block cipher
that look similar but can be quickly broken. 1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 58 10
How do we know that AES and ChaCha20 are PRFs? We don’t. We conjecture security after enough failed attack efforts. “All of these attacks fail and we don’t have better attack ideas.” Remaining slides today:
- Simple example of block cipher.
Seems to be a good cipher, except block size is too small.
- Variants of this block cipher
that look similar but can be quickly broken.
11
1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 59 10
do we know that AES and ChaCha20 are PRFs? We don’t. conjecture security enough failed attack efforts.
- f these attacks fail and we
have better attack ideas.” Remaining slides today: Simple example of block cipher. Seems to be a good cipher, except block size is too small. riants of this block cipher look similar but be quickly broken.
11
1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
uint32: representing integer b +: addition c += d: ^: xor; ⊕ each bit Lower precedence so spacing <<4: multiplication (0; 0; 0; 0 >>5: division (b5; b6; :

SLIDE 60
10
that AES and PRFs? We don’t. security ailed attack efforts. attacks fail and we etter attack ideas.” today: example of block cipher. good cipher, size is too small. this block cipher similar but broken.
11
1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
uint32: 32 bits (b representing the “unsigned” integer b0 + 2b1 + +: addition mod 2 c += d: same as c ^: xor; ⊕; addition each bit separately Lower precedence so spacing is not misleading. <<4: multiplication (0; 0; 0; 0; b0; b1; : : >>5: division by 32, (b5; b6; : : : ; b31; 0;

SLIDE 61
10
AES and don’t. efforts. and we ideas.” cipher. cipher, small. cipher
11
1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
uint32: 32 bits (b0; b1; : : : ; representing the “unsigned” integer b0 + 2b1 + · · · + 231b +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0).

SLIDE 62
11
1994 Wheeler–Needham “TEA, a tiny encryption algorithm”:
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0).

SLIDE 63
11
Wheeler–Needham “TEA, encryption algorithm”:
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0). Functionalit TEA is a with a 128-bit

SLIDE 64
11
Wheeler–Needham “TEA, algorithm”:
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0). Functionality TEA is a 64-bit blo with a 128-bit key

SLIDE 65
11
“TEA, rithm”:
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0). Functionality TEA is a 64-bit block cipher with a 128-bit key.

SLIDE 66
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key.

SLIDE 67
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]).

SLIDE 68
12
uint32: 32 bits (b0; b1; : : : ; b31) representing the “unsigned” integer b0 + 2b1 + · · · + 231b31. +: addition mod 232. c += d: same as c = c + d. ^: xor; ⊕; addition of each bit separately mod 2. Lower precedence than + in C, so spacing is not misleading. <<4: multiplication by 16, i.e., (0; 0; 0; 0; b0; b1; : : : ; b27). >>5: division by 32, i.e., (b5; b6; : : : ; b31; 0; 0; 0; 0; 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]). Can efficiently encrypt: (key; plaintext) → ciphertext. Can efficiently decrypt: (key; ciphertext) → plaintext.

SLIDE 69
12
: 32 bits (b0; b1; : : : ; b31) resenting the “unsigned” integer b0 + 2b1 + · · · + 231b31. addition mod 232. : same as c = c + d. r; ⊕; addition of bit separately mod 2. precedence than + in C, spacing is not misleading. multiplication by 16, i.e., ; 0; b0; b1; : : : ; b27). division by 32, i.e., ; : : : ; b31; 0; 0; 0; 0; 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]). Can efficiently encrypt: (key; plaintext) → ciphertext. Can efficiently decrypt: (key; ciphertext) → plaintext. Wait, ho
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 70
12
(b0; b1; : : : ; b31) “unsigned” + · · · + 231b31. 232. c = c + d. addition of rately mod 2. recedence than + in C, not misleading. multiplication by 16, i.e., : : : ; b27). 32, i.e., 0; 0; 0; 0; 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]). Can efficiently encrypt: (key; plaintext) → ciphertext. Can efficiently decrypt: (key; ciphertext) → plaintext. Wait, how can we
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 71
12
: ; b31) “unsigned”
31b31.
. 2. in C, misleading. i.e., 0).
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]). Can efficiently encrypt: (key; plaintext) → ciphertext. Can efficiently decrypt: (key; ciphertext) → plaintext. Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 72
13
Functionality TEA is a 64-bit block cipher with a 128-bit key. Input: 128-bit key (namely k[0],k[1],k[2],k[3]); 64-bit plaintext (b[0],b[1]). Output: 64-bit ciphertext (final b[0],b[1]). Can efficiently encrypt: (key; plaintext) → ciphertext. Can efficiently decrypt: (key; ciphertext) → plaintext.
14
Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 73
13
unctionality is a 64-bit block cipher 128-bit key. 128-bit key (namely k[0],k[1],k[2],k[3]); plaintext (b[0],b[1]). Output: 64-bit ciphertext b[0],b[1]). efficiently encrypt: plaintext) → ciphertext. efficiently decrypt: ciphertext) → plaintext.
14
Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Answer:
void decrypt(uint32 { uint32 uint32 for (r y -= x -= c -= } b[0] = }

SLIDE 74
13
block cipher key. ey (namely k[0],k[1],k[2],k[3]); (b[0],b[1]). ciphertext ). encrypt: → ciphertext. decrypt: → plaintext.
14
Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Answer: Each step
void decrypt(uint32 { uint32 x = b[0], uint32 r, c = 32 for (r = 0;r < y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] }

SLIDE 75
13
cipher (namely b[0],b[1]). ciphertext ciphertext. plaintext.
14
Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }

SLIDE 76
14
Wait, how can we decrypt?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
15
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += 1) { y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }

SLIDE 77
14
how can we decrypt?
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
15
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += 1) { y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }
Generalization, (used in, 1973 Feistel–Copp
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption,
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);

SLIDE 78
14
e decrypt?
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
15
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += 1) { y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }
Generalization, Feistel (used in, e.g., “Lucifer” 1973 Feistel–Copp
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);

SLIDE 79
14
decrypt?
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
15
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += 1) { y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }
Generalization, Feistel netw (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);

SLIDE 80
15
Answer: Each step is invertible.
void decrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; for (r = 0;r < 32;r += 1) { y -= x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; x -= y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; c -= 0x9e3779b9; } b[0] = x; b[1] = y; }
16
Generalization, Feistel network (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);

SLIDE 81 15
er: Each step is invertible.
decrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 32 * 0x9e3779b9; (r = 0;r < 32;r += 1) {
^ (x>>5)+k[3];
^ (y>>5)+k[1];
= x; b[1] = y;
16
Generalization, Feistel network (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);
TEA again
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 82
15
step is invertible.
decrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 32 * 0x9e3779b9; 32;r += 1) { (x<<4)+k[2] (x>>5)+k[3]; (y<<4)+k[0] (y>>5)+k[1]; 0x9e3779b9; = y;
16
Generalization, Feistel network (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);
TEA again for compa
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 83
15
invertible.
*b,uint32 *k) b[1]; 0x9e3779b9; 1) { (x<<4)+k[2] (x>>5)+k[3]; (y<<4)+k[0] (y>>5)+k[1];
16
Generalization, Feistel network (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);
TEA again for comparison
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 84
16
Generalization, Feistel network (used in, e.g., “Lucifer” from 1973 Feistel–Coppersmith):
x += function1(y,k); y += function2(x,k); x += function3(y,k); y += function4(x,k); ...
Decryption, inverting each step:
... y -= function4(x,k); x -= function3(y,k); y -= function2(x,k); x -= function1(y,k);
17
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 85
16
Generalization, Feistel network in, e.g., “Lucifer” from eistel–Coppersmith):
function1(y,k); function2(x,k); function3(y,k); function4(x,k);
Decryption, inverting each step:
function4(x,k); function3(y,k); function2(x,k); function1(y,k);
17
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
XORTEA:
void encrypt(uint32 { uint32 uint32 for (r c += x ^= y ^= } b[0] = }

SLIDE 86
16
Feistel network “Lucifer” from eistel–Coppersmith):
function1(y,k); function2(x,k); function3(y,k); function4(x,k);
inverting each step:
function4(x,k); function3(y,k); function2(x,k); function1(y,k);
17
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
XORTEA: a bad cipher
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] }

SLIDE 87
16
network from mith): step:
17
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }

SLIDE 88
17
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }

SLIDE 89
17
again for comparison
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
“Hardwa xor circuit

SLIDE 90
17
comparison
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
“Hardware-friendlier” xor circuit is cheap

SLIDE 91
17
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
“Hardware-friendlier” cipher, xor circuit is cheaper than add.

SLIDE 92
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add.

SLIDE 93
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits!

SLIDE 94
18
XORTEA: a bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; y ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; } b[0] = x; b[1] = y; }
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.

SLIDE 95
18
ORTEA: a bad cipher
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; ^= y^c ^ (y<<4)^k[0] ^ (y>>5)^k[1]; ^= x^c ^ (x<<4)^k[2] ^ (x>>5)^k[3]; = x; b[1] = y;
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62. There is with coefficients such that, XORTEA

SLIDE 96
18
cipher
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)^k[0] (y>>5)^k[1]; (x<<4)^k[2] (x>>5)^k[3]; = y;
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62. There is a matrix M with coefficients in such that, for all (k XORTEAk(b) = (1

SLIDE 97
18
*b,uint32 *k) b[1]; 1) { (y<<4)^k[0] (y>>5)^k[1]; (x<<4)^k[2] (x>>5)^k[3];
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62. There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M.

SLIDE 98
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M.

SLIDE 99
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M.

SLIDE 100
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4).

SLIDE 101
19
“Hardware-friendlier” cipher, since xor circuit is cheaper than add. But output bits are linear functions of input bits! e.g. First output bit is 1⊕k0 ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕ k20 ⊕ k21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k42 ⊕ k43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k64 ⊕ k67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k96⊕k99⊕k101⊕k108⊕k117⊕k126⊕ b1⊕b3⊕b10⊕b12⊕b21⊕b30⊕b32⊕ b33 ⊕b35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕ b44 ⊕ b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4). This breaks PRP (and PRF): uniform random permutation (or function) F almost never has F(b1) ⊕ F(b2) = F(b3) ⊕ F(b4).

SLIDE 102 19
rdware-friendlier” cipher, since circuit is cheaper than add.
functions of input bits! First output bit is ⊕k1 ⊕k3 ⊕k10 ⊕k11 ⊕k12 ⊕
21 ⊕ k30 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ 43 ⊕ k44 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ 67 ⊕ k69 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ 99⊕k101⊕k108⊕k117⊕k126⊕
⊕b10⊕b12⊕b21⊕b30⊕b32⊕
35 ⊕b37 ⊕b39 ⊕b42 ⊕b43 ⊕
b47 ⊕ b52 ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4). This breaks PRP (and PRF): uniform random permutation (or function) F almost never has F(b1) ⊕ F(b2) = F(b3) ⊕ F(b4). TEA again
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 103
19
re-friendlier” cipher, since cheaper than add. are linear ut bits! bit is ⊕k10 ⊕k11 ⊕k12 ⊕ k32 ⊕ k33 ⊕ k35 ⊕ k52 ⊕ k53 ⊕ k62 ⊕ k76 ⊕ k85 ⊕ k94 ⊕ k108⊕k117⊕k126⊕ ⊕b21⊕b30⊕b32⊕ b39 ⊕b42 ⊕b43 ⊕ ⊕ b53 ⊕ b57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4). This breaks PRP (and PRF): uniform random permutation (or function) F almost never has F(b1) ⊕ F(b2) = F(b3) ⊕ F(b4). TEA again for compa
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 104
19
cipher, since add. ⊕k12 ⊕ ⊕ k35 ⊕ ⊕ k62 ⊕ ⊕ k94 ⊕ ⊕k126⊕
30⊕b32⊕
⊕b43 ⊕
57 ⊕ b62.
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4). This breaks PRP (and PRF): uniform random permutation (or function) F almost never has F(b1) ⊕ F(b2) = F(b3) ⊕ F(b4). TEA again for comparison
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 105
20
There is a matrix M with coefficients in F2 such that, for all (k; b), XORTEAk(b) = (1; k; b)M. XORTEAk(b1) ⊕ XORTEAk(b2) = (0; 0; b1 ⊕ b2)M. Very fast attack: if b4 = b1 ⊕ b2 ⊕ b3 then XORTEAk(b1)⊕XORTEAk(b2) = XORTEAk(b3) ⊕ XORTEAk(b4). This breaks PRP (and PRF): uniform random permutation (or function) F almost never has F(b1) ⊕ F(b2) = F(b3) ⊕ F(b4).
21
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 106
20
is a matrix M coefficients in F2 that, for all (k; b), ORTEAk(b) = (1; k; b)M. ORTEAk(b1) ⊕ XORTEAk(b2) ; b1 ⊕ b2)M. fast attack: b1 ⊕ b2 ⊕ b3 then ORTEAk(b1)⊕XORTEAk(b2) = ORTEAk(b3) ⊕ XORTEAk(b4). reaks PRP (and PRF): random permutation unction) F almost never has ⊕ F(b2) = F(b3) ⊕ F(b4).
21
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
LEFTEA:
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 107
20
matrix M in F2 all (k; b), (1; k; b)M. XORTEAk(b2) M. attack: ⊕ b3 then XORTEAk(b2) = XORTEAk(b4). (and PRF): permutation almost never has F(b3) ⊕ F(b4).
21
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
LEFTEA: another
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] }

SLIDE 108
20
. ORTEAk(b2)
k(b2) =
ORTEAk(b4). PRF): ermutation never has F(b4).
21
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 109
21
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 110
21
again for comparison
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
Addition but addition First output 1 ⊕ k0 ⊕

SLIDE 111
21
comparison
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
Addition is not F2-linea but addition mod 2 First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64

SLIDE 112
21
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
Addition is not F2-linear, but addition mod 2 is F2-linea First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b

SLIDE 113
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32.

SLIDE 114
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit.

SLIDE 115
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits.

SLIDE 116
22
LEFTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; } b[0] = x; b[1] = y; }
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits. (Diffusion from low bits to high bits: <<4; carries in addition.)

SLIDE 117
22
LEFTEA: another bad cipher
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y<<5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x<<5)+k[3]; = x; b[1] = y;
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits. (Diffusion from low bits to high bits: <<4; carries in addition.) TEA again
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 118
22
another bad cipher
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y<<5)+k[1]; (x<<4)+k[2] (x<<5)+k[3]; = y;
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits. (Diffusion from low bits to high bits: <<4; carries in addition.) TEA again for compa
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 119
22
cipher
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y<<5)+k[1]; (x<<4)+k[2] (x<<5)+k[3];
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits. (Diffusion from low bits to high bits: <<4; carries in addition.) TEA again for comparison
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 120
23
Addition is not F2-linear, but addition mod 2 is F2-linear. First output bit is 1 ⊕ k0 ⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32. Higher output bits are increasingly nonlinear but they never affect first bit. How TEA avoids this problem: >>5 diffuses nonlinear changes from high bits to low bits. (Diffusion from low bits to high bits: <<4; carries in addition.)
24
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 121 23
Addition is not F2-linear, addition mod 2 is F2-linear.
⊕ k32 ⊕ k64 ⊕ k96 ⊕ b32.
reasingly nonlinear they never affect first bit. TEA avoids this problem: diffuses nonlinear changes high bits to low bits. (Diffusion from low bits to high <<4; carries in addition.)
24
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
TEA4: another
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 122
23
F2-linear, d 2 is F2-linear. is
64 ⊕ k96 ⊕ b32.
bits nonlinear affect first bit. avoids this problem: nonlinear changes low bits. low bits to high ries in addition.)
24
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
TEA4: another bad
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 123 23
b32. bit. roblem: changes high addition.)
24
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 124
24
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 125
24
again for comparison
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Fast attack: TEA4k(x TEA4k(x

SLIDE 126
24
comparison
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Fast attack: TEA4k(x + 231; y) TEA4k(x; y) have

SLIDE 127
24
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first

SLIDE 128
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit.

SLIDE 129
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20.

SLIDE 130
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2.

SLIDE 131
25
TEA4: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 4;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4.

SLIDE 132
25
TEA4: another bad cipher
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 4;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4. More sophisticated trace probabilities probabilities probabilities differences C(x + ‹) Use algeb non-randomness

SLIDE 133
25
bad cipher
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 4;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4. More sophisticated trace probabilities probabilities of linea probabilities of higher-o differences C(x + ‹ C(x + ‹) − C(x + Use algebra+statistics non-randomness in

SLIDE 134
25
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4. More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); Use algebra+statistics to exploit non-randomness in probabilities.

SLIDE 135
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities.

SLIDE 136
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA.

SLIDE 137
26
Fast attack: TEA4k(x + 231; y) and TEA4k(x; y) have same first bit. Trace x; y differences through steps in computation. r = 0: multiples of 231; 226. r = 1: multiples of 221; 216. r = 2: multiples of 211; 26. r = 3: multiples of 21; 20. Uniform random function F: F(x + 231; y) and F(x; y) have same first bit with probability 1=2. PRF advantage 1=2. Two pairs (x; y): advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA. Hard question in cipher design: How many “rounds” are really needed for security?

SLIDE 138
26
attack: (x + 231; y) and (x; y) have same first bit. x; y differences through steps in computation. multiples of 231; 226. multiples of 221; 216. multiples of 211; 26. multiples of 21; 20. rm random function F: 231; y) and F(x; y) have first bit with probability 1=2. advantage 1=2. pairs (x; y): advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA. Hard question in cipher design: How many “rounds” are really needed for security? TEA again
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 139 26
y) and have same first bit. differences computation.
- f 231; 226.
- f 221; 216.
- f 211; 26.
- f 21; 20.
function F: and F(x; y) have with probability 1=2. 1=2. ): advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA. Hard question in cipher design: How many “rounds” are really needed for security? TEA again for compa
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 140 26
first bit. computation.
26. 16.
. F: have
advantage 3=4.
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA. Hard question in cipher design: How many “rounds” are really needed for security? TEA again for comparison
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 141
27
More sophisticated attacks: trace probabilities of differences; probabilities of linear equations; probabilities of higher-order differences C(x + ‹ + ›) − C(x + ‹) − C(x + ›) + C(x); etc. Use algebra+statistics to exploit non-randomness in probabilities. Attacks get beyond r = 4 but rapidly lose effectiveness. Very far from full TEA. Hard question in cipher design: How many “rounds” are really needed for security?
28
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 142
27
sophisticated attacks: probabilities of differences; robabilities of linear equations; robabilities of higher-order differences C(x + ‹ + ›) − ‹) − C(x + ›) + C(x); etc. algebra+statistics to exploit non-randomness in probabilities. ttacks get beyond r = 4 rapidly lose effectiveness. far from full TEA. question in cipher design: many “rounds” are needed for security?
28
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEA:
void encrypt(uint32 { uint32 uint32 for (r x += y += } b[0] = }

SLIDE 143 27
sophisticated attacks: robabilities of differences; linear equations; higher-order ‹ + ›) − + ›) + C(x); etc. ra+statistics to exploit in probabilities.
effectiveness. full TEA. cipher design: “rounds” are security?
28
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEA: another
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0x9e3779b9; for (r = 0;r < x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 144
27
attacks: differences; equations; rder x); etc. exploit robabilities. effectiveness. design:
28
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 145
28
TEA again for comparison
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 146
28
again for comparison
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEA where Ik

SLIDE 147
28
comparison
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEAk(b) = I1000
k
where Ik does x+=...;y+=...

SLIDE 148
28
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=...

SLIDE 149
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=....

SLIDE 150
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b).

SLIDE 151
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)).

SLIDE 152
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.)

SLIDE 153
29
REPTEA: another bad cipher
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; for (r = 0;r < 1000;r += 1) { x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.) This is a slide attack. TEA avoids this by varying c.

SLIDE 154
29
REPTEA: another bad cipher
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0x9e3779b9; (r = 0;r < 1000;r += 1) { += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.) This is a slide attack. TEA avoids this by varying c. What ab
void encrypt(uint32 { uint32 uint32 for (r c += x += y += } b[0] = }

SLIDE 155
29
another bad cipher
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0x9e3779b9; 1000;r += 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.) This is a slide attack. TEA avoids this by varying c. What about original
void encrypt(uint32 { uint32 x = b[0], uint32 r, c = 0; for (r = 0;r < c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] }

SLIDE 156
29
cipher
*b,uint32 *k) b[1]; 0x9e3779b9; += 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.) This is a slide attack. TEA avoids this by varying c. What about original TEA?
void encrypt(uint32 *b,uint32 { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 157
30
REPTEAk(b) = I1000
k
(b) where Ik does x+=...;y+=.... Try list of 232 inputs b. Collect outputs REPTEAk(b). Good chance that some b in list also has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). For each (b; a) from list: Try solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) to figure out k. (More equations: try re-encrypting these outputs.) This is a slide attack. TEA avoids this by varying c.
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }

SLIDE 158
30
REPTEAk(b) = I1000
k
(b) Ik does x+=...;y+=.... list of 232 inputs b. Collect outputs REPTEAk(b). chance that some b in list has a = Ik(b) in list. Then REPTEAk(a)=Ik(REPTEAk(b)). each (b; a) from list: solving equations a = Ik(b), REPTEAk(a)=Ik(REPTEAk(b)) figure out k. (More equations: re-encrypting these outputs.) a slide attack. avoids this by varying c.
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Related k TEAk′(b where (k (k[0] + 2

SLIDE 159
30
I1000
k
(b) x+=...;y+=.... inputs b. REPTEAk(b). that some b in list b) in list. Then (REPTEAk(b)). from list: equations a = Ik(b), (REPTEAk(b)) (More equations: these outputs.) attack. by varying c.
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Related keys: e.g., TEAk′(b) = TEAk where (k′[0]; k′[1]; (k[0] + 231; k[1] +

SLIDE 160 30
x+=...;y+=.... (b). in list Then (REPTEAk(b)). Ik(b), (REPTEAk(b)) equations:
g c.
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) (k[0] + 231; k[1] + 231; k[2]; k

SLIDE 161
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]).

SLIDE 162
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack?

SLIDE 163
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation.

SLIDE 164
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs.

SLIDE 165
31
What about original TEA?
void encrypt(uint32 *b,uint32 *k) { uint32 x = b[0], y = b[1]; uint32 r, c = 0; for (r = 0;r < 32;r += 1) { c += 0x9e3779b9; x += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; y += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; } b[0] = x; b[1] = y; }
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small.

SLIDE 166
31
about original TEA?
encrypt(uint32 *b,uint32 *k) uint32 x = b[0], y = b[1]; uint32 r, c = 0; (r = 0;r < 32;r += 1) { += 0x9e3779b9; += y+c ^ (y<<4)+k[0] ^ (y>>5)+k[1]; += x+c ^ (x<<4)+k[2] ^ (x>>5)+k[3]; = x; b[1] = y;
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small. 1997 Kelse Fancier relationship has chance a particula

SLIDE 167
31
riginal TEA?
encrypt(uint32 *b,uint32 *k) b[0], y = b[1]; 0; 32;r += 1) { 0x9e3779b9; (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3]; = y;
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small. 1997 Kelsey–Schne Fancier relationship has chance 2−11 of a particular output

SLIDE 168
31
*b,uint32 *k) b[1]; 1) { (y<<4)+k[0] (y>>5)+k[1]; (x<<4)+k[2] (x>>5)+k[3];
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small. 1997 Kelsey–Schneier–Wagner: Fancier relationship between has chance 2−11 of producing a particular output equation.

SLIDE 169
32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation.

SLIDE 170 32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis

SLIDE 171 32
Related keys: e.g., TEAk′(b) = TEAk(b) where (k′[0]; k′[1]; k′[2]; k′[3]) = (k[0] + 231; k[1] + 231; k[2]; k[3]). Is this an attack? PRP attack goal: distinguish TEAk, for one secret key k, from uniform random permutation. Brute-force attack: Guess key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with chance 2−126. Still very small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis
But advertised as “related-key cryptanalysis” and claimed to justify recommendations for designers regarding key scheduling.

SLIDE 172 32
Related keys: e.g., (b) = TEAk(b) (k′[0]; k′[1]; k′[2]; k′[3]) = 231; k[1] + 231; k[2]; k[3]). an attack? attack goal: distinguish , for one secret key k, from random permutation. Brute-force attack: key g, see if TEAg matches TEAk on some outputs. Related keys ⇒ g succeeds with 2−126. Still very small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis
But advertised as “related-key cryptanalysis” and claimed to justify recommendations for designers regarding key scheduling. Some wa about cipher hash-function Take upcoming “Selected Includes Read attack especially Try to break e.g., find Reasonable 2000 Schneier in block-cipher

SLIDE 173 32
e.g., Ak(b) [1]; k′[2]; k′[3]) = + 231; k[2]; k[3]). attack? goal: distinguish secret key k, from permutation. attack: if TEAg
g succeeds with Still very small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis
But advertised as “related-key cryptanalysis” and claimed to justify recommendations for designers regarding key scheduling. Some ways to learn about cipher attacks, hash-function attacks, Take upcoming course “Selected areas in Includes symmetric Read attack papers, especially from FS Try to break ciphers e.g., find attacks on Reasonable starting 2000 Schneier “Self-study in block-cipher cryptanalysis”.

SLIDE 174 32
[3]) = [2]; k[3]). distinguish k, from ermutation.
succeeds with small.
33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis
But advertised as “related-key cryptanalysis” and claimed to justify recommendations for designers regarding key scheduling. Some ways to learn more about cipher attacks, hash-function attacks, etc.: Take upcoming course “Selected areas in cryptology”. Includes symmetric attacks. Read attack papers, especially from FSE conference. Try to break ciphers yourself: e.g., find attacks on FEAL. Reasonable starting point: 2000 Schneier “Self-study course in block-cipher cryptanalysis”.

SLIDE 175 33
1997 Kelsey–Schneier–Wagner: Fancier relationship between k; k′ has chance 2−11 of producing a particular output equation. No evidence in literature that this helps brute-force attack,
- r otherwise affects PRP security.
No challenge to security analysis
But advertised as “related-key cryptanalysis” and claimed to justify recommendations for designers regarding key scheduling.
34
Some ways to learn more about cipher attacks, hash-function attacks, etc.: Take upcoming course “Selected areas in cryptology”. Includes symmetric attacks. Read attack papers, especially from FSE conference. Try to break ciphers yourself: e.g., find attacks on FEAL. Reasonable starting point: 2000 Schneier “Self-study course in block-cipher cryptanalysis”.