1
Virtual Memory
Chapter 18
- S. Dandamudi
2003
To be used with S. Dandamudi, “Fundamentals of Computer Organization and Design,” Springer, 2003.
S. Dandamudi Chapter 18: Page 2
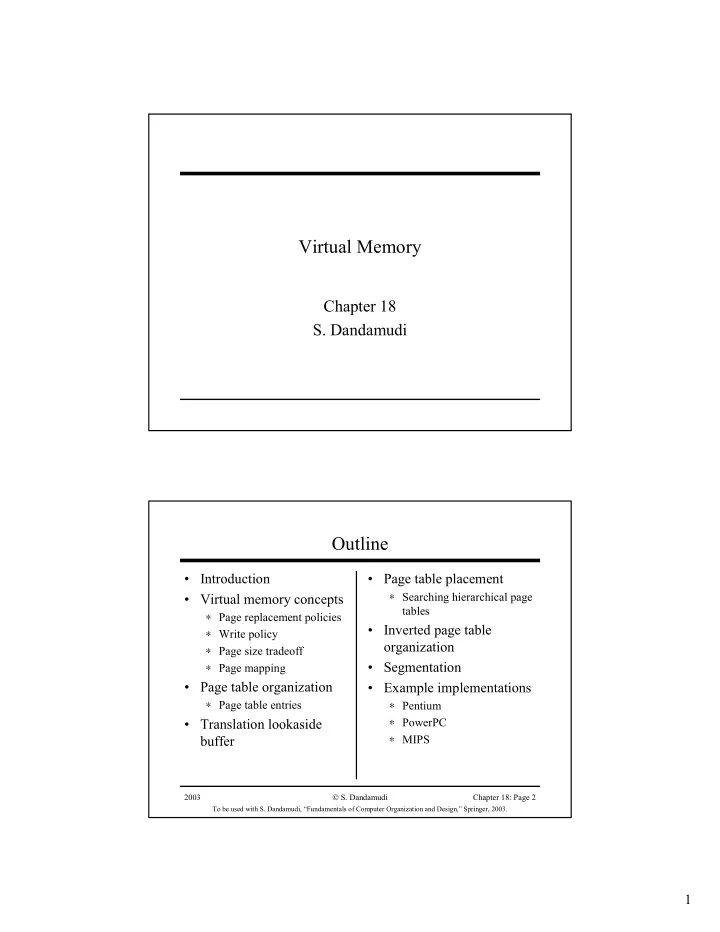
Outline
- Introduction
- Virtual memory concepts
∗ Page replacement policies ∗ Write policy ∗ Page size tradeoff ∗ Page mapping
- Page table organization
∗ Page table entries
- Translation lookaside
buffer
- Page table placement
∗ Searching hierarchical page tables
- Inverted page table
- rganization
- Segmentation
- Example implementations