SLIDE 1
1
The Discrete Logarithm Problem
Debdeep Mukhopadhyay IIT Kharagpur
The DLP Problem
- Consider αεG, having order n.
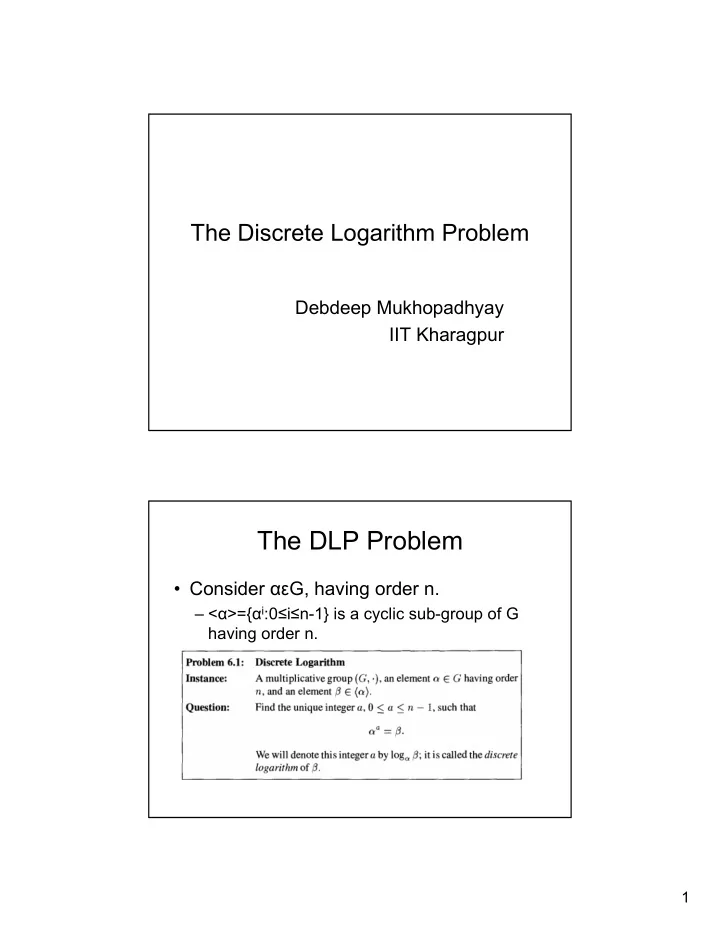
The DLP Problem Consider G, having order n. < >={ i :0 i - - PDF document
The Discrete Logarithm Problem Debdeep Mukhopadhyay IIT Kharagpur The DLP Problem Consider G, having order n. < >={ i :0 i n-1} is a cyclic sub-group of G having order n. 1 Cryptographic Utility of DLP For
*. Note 809 is
*.
L1: L2: