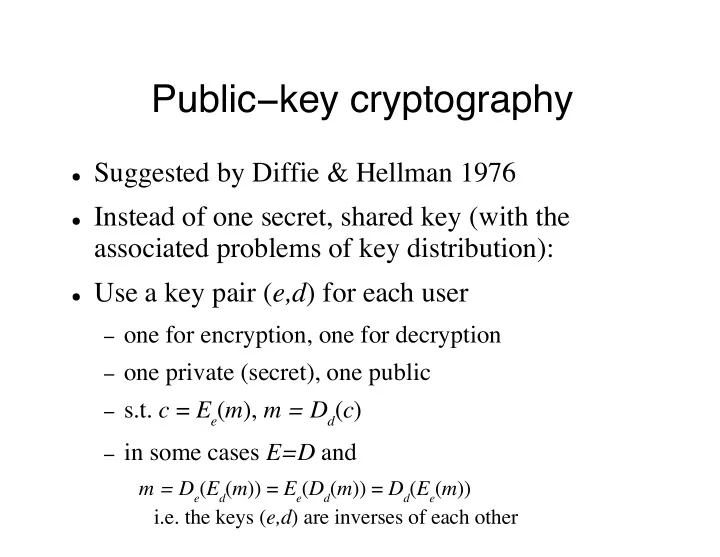
Public!key cryptography
S"##ested )y Diffie . /ellman 1567 8nstead 9f 9ne secret, s=ared key ?@it= t=e
ass9ciated pr9)lems 9f key distri)"ti9n)C
Dse a key pair ?e,d) f9r eac= "ser
9ne f9r encrypti9n, 9ne f9r decrypti9n 9ne priEate ?secret), 9ne p")lic sFtF c = Ee?m), m = Dd?c) in s9me cases E=D and