Università degli Studi di Roma “Tor Vergata” Dipartimento di Ingegneria Civile e Ingegneria Informatica
NoSQL Databases
Corso di Sistemi e Architetture per Big Data A.A. 2016/17 Valeria Cardellini
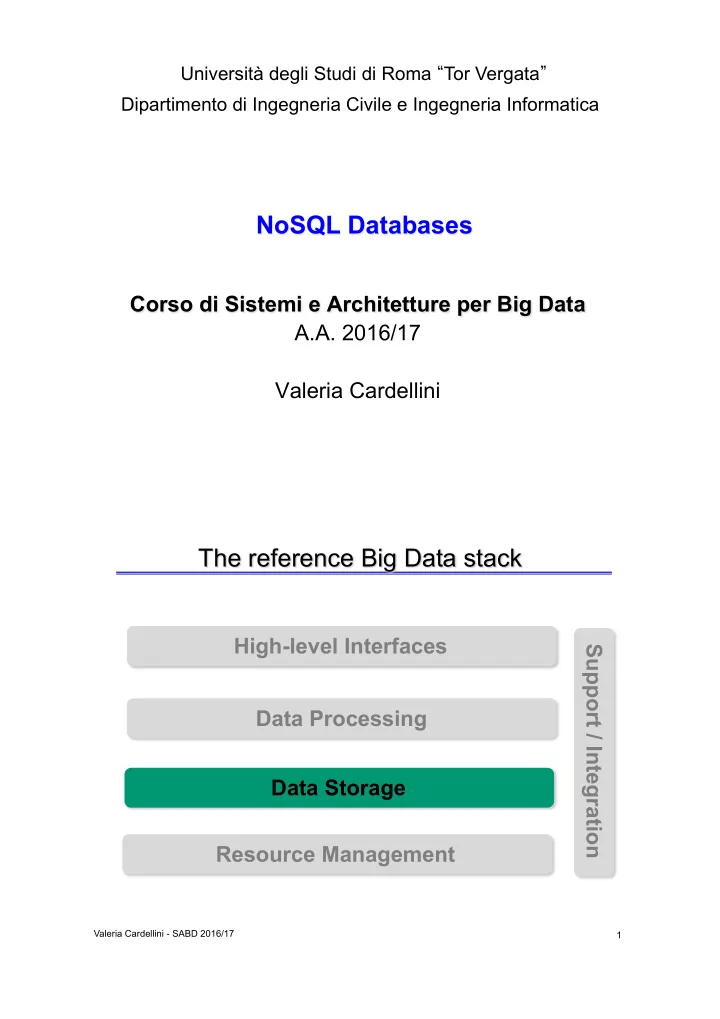
The reference Big Data stack
Valeria Cardellini - SABD 2016/17 1