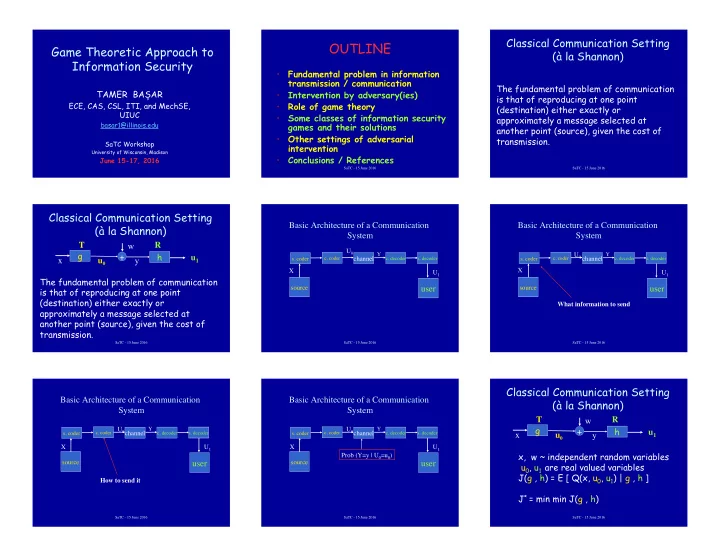
Game Theoretic Approach to Information Security
TAMER BAȘAR
ECE, CAS, CSL, ITI, and MechSE, UIUC
basar1@illinois.edu SaTC Workshop
University of Wisconsin, Madison
June 15-17, 2016
SaTC - 15 June 2016
OUTLINE!
- Fundamental problem in information
transmission / communication
- Intervention by adversary(ies)
- Role of game theory
- Some classes of information security
games and their solutions
- Other settings of adversarial
intervention
- Conclusions / References
SaTC - 15 June 2016
Classical Communication Setting (à la Shannon)
The fundamental problem of communication is that of reproducing at one point (destination) either exactly or approximately a message selected at another point (source), given the cost of transmission.
SaTC - 15 June 2016
Classical Communication Setting (à la Shannon)
g h + w y u0 u1 x The fundamental problem of communication is that of reproducing at one point (destination) either exactly or approximately a message selected at another point (source), given the cost of transmission. T R
SaTC - 15 June 2016
Basic Architecture of a Communication System
- s. coder
channel
user
U1
- c. coder
- c. decoder
- s. decoder
source U0
Y
X
SaTC - 15 June 2016
Basic Architecture of a Communication System
- s. coder
channel
user
U1
- c. coder
- c. decoder
- s. decoder
source U0
Y
X What information to send
SaTC - 15 June 2016
Basic Architecture of a Communication System
- s. coder
channel
user
U1
- c. coder
- c. decoder
- s. decoder
source U0
Y
X How to send it
SaTC - 15 June 2016
Basic Architecture of a Communication System
- s. coder
channel
user
U1
- c. coder
- c. decoder
- s. decoder
source U0
Y
X Prob (Y=y | U0=u0)
SaTC - 15 June 2016