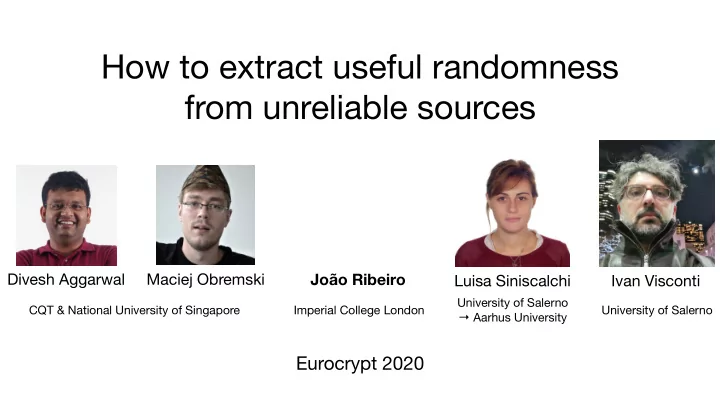
How to extract useful randomness from unreliable sources
Eurocrypt 2020
Divesh Aggarwal Maciej Obremski Luisa Siniscalchi
University of Salerno → Aarhus University
João Ribeiro
Imperial College London CQT & National University of Singapore
Ivan Visconti
University of Salerno