Efficient Multi-Match Packet Classification with TCAM
Fang Yu and Randy H. Katz zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
Abstract- Today's packet classification systems are designed to
provide the highest priority matching result, e.g., the longest prefix match, even if a packet matches multiple classification
- rules. However, new network applications, such as intrusion
detection systems, require information about all the matching
- results. We call this the multi-mtch classijication zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
problem In
several complex network applications, multi-match classification is immediately followed by other processing dependent on the classification results. Therefore, classification should be even faster than the line rate. Pure software solutions cannot be used due to their slow speeds.
In this paper, we present a solution based on Ternary Content
Addressable Memory (TCAM), which produces multi-match classification results with only one TCAM lookup and one SRAM lookup per packet- about ten times fewer memory lookups than
a pure software approach. In addition, we present a scheme to
remove the negation format in rule sets, which can save u p to
95% of TCAM space compared with the straight forward
- solution. We show that using the pre-processing scheme we
present, header processing for the SNORT rule set can be done with one TCAM and one SRAM lookup using a zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
135KB
TCAM.
Index Term-Packet Classification, Multi-Match Packet
Classification, Ternary CAM, Negation Removing. zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
- I. INTRODUCTION
ew network applications are emerging that demand multi- match classification, that is, requiring all matching results instead of only the highest priority match. One example
- f such an application is the network intrusion detection
system, which monitors packets in a network and detects malicious intrusions or DOS attacks. Systems like SNORT
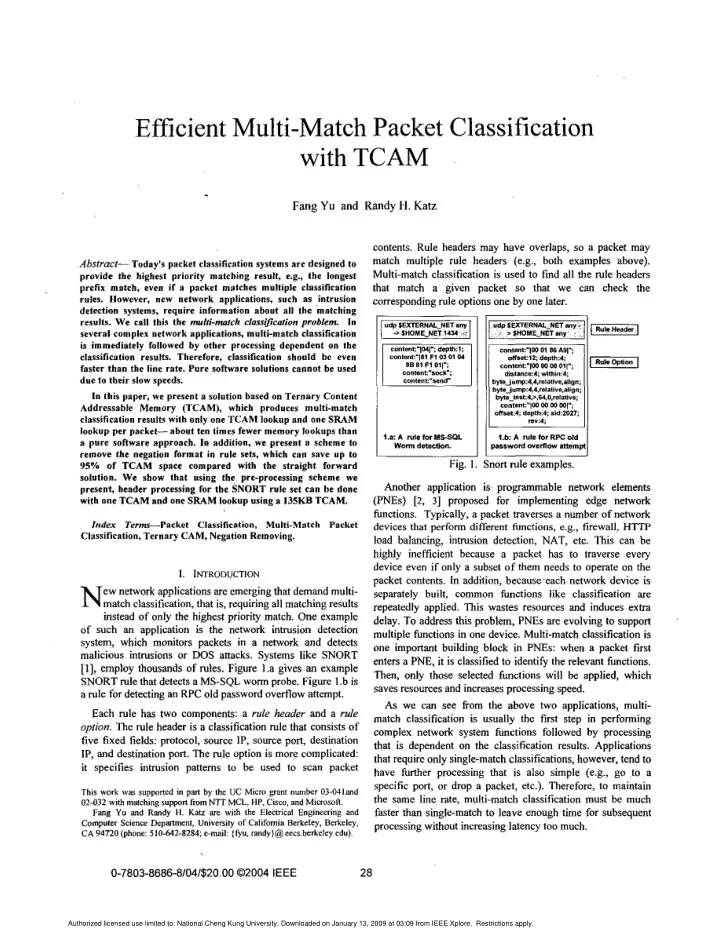
[I], employ thousands of rules. Figure 1.a gives an example SNORT rule that detects a MS-SQL worm probe. Figure zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
1 .b is
a rule for detecting an RPC old password overflow attempt. Each rule has two components: a rule header and a rule zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
@on.
The rule header is a classification rule that consists of five fixed fields: protocol, source IP, source port, destination IP, and destination port. The rule option is more complicated: it specifies intrusion patterns to be used to scan packet This work was
supported in pm by the UC zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA Micro @ant number 03-041and 02-032 with matching support fromNTTMCL, HP, Cisco, and Microson. Fang Yu and Randy H. Katz are with the Electrical Engineering and Computer Science Depmtmenf, University of California Berkeley, Berkeley, CA 94720 (phone: 510-642-8284; e-mail: (&U, randy)@ eecs.berkeley.edu).
N
- contents. Rule headers may have overlaps, zyxwvutsrqponmlkjihgfedcbaZYXWVUTSRQPONMLKJIHGFEDCBA
so a packet may
match multiple rule headers (e.g., both examples above). Multi-match classification is used to fmd all the rule headers that match a given packet so that we can check the corresponding rule options one by one later.
contmt:~p4l":
daplh.1; contenl'"l81 F1 0) 01 04 O B $1 F1 0117
I
cO"lB"t:--K-:
I
conten1:"lW 01 86 AOl"; 0ffset:lZ: depth4
1.a: A rule for MSSQL 1.b A rule for RPC Old
- Fig. 1. Snort rule examples.
Another application is. proganunable network elements (PNEs) [2, 31 proposed for implementing edge network
- functions. Typically, a packet traverses a number of network
devices that perform different functions, e.g., firewall, HTTP load balancing, intrusion detection, NAT, etc. This can be highly inefficient because a packet has to traverse every device even if only a subset of them needs to operate on the packet contents. In addition, becauweach network device is separately built, common functions like classification are repeatedly applied. This wastes resources and induces extra
- delay. To address this problem, PNEs are evolving to support
multiple functions in one device. Multi-match classification is
- ne important building block in PNEs: when a packet first
enters a PNE, it is classified to identify the relevant functions. Then, only those selected functions will be applied, which saves resources and increases processing speed. As we can see !?om the above two applications, multi- match classification is usually the fmt step in performing complex network system functions followed by processing that is dependent on the classification results. Applications that require only single-match classifications, however, tend to have further processing that is also simple (e.g., go to a specific port, or drop a packet, etc.). Therefore, to maintain the same line rate, multi-match classification must be much faster than single-match to leave enough time for subsequent processing without increasing latency too much.
0-7803-8686-8/04/$20.00
02004 IEEE 28
Authorized licensed use limited to: National Cheng Kung University. Downloaded on January 13, 2009 at 03:09 from IEEE Xplore. Restrictions apply.