OPERATING SYSTEMS OPERATING SYSTEMS
Design and Implementation Instructor:
Hadi Salimi Hadi Salimi Computer Engineering Department IRAN University of Science and Technology hsalimi@iust ac ir hsalimi@iust.ac.ir
Deadlocks (cont ) Deadlocks (cont.)
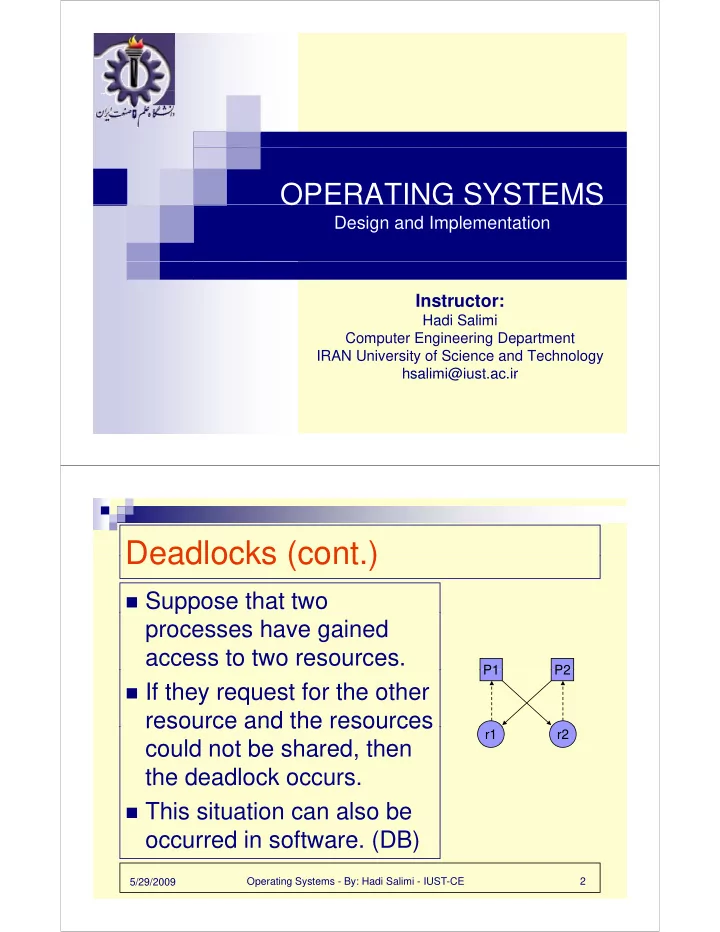
Suppose that two
pp processes have gained access to two resources.
P2 P1
If they request for the other
resource and the resources
P2 P1
resource and the resources could not be shared, then the deadlock occurs.
r2 r1
the deadlock occurs.
This situation can also be
- ccurred in software (DB)
Operating Systems - By: Hadi Salimi - IUST-CE 2 5/29/2009
- ccurred in software. (DB)