computation may someday be organized as a public utility John - - PowerPoint PPT Presentation
computation may someday be organized as a public utility John - - PowerPoint PPT Presentation
Security and Cloud Computing computation may someday be organized as a public utility John McCarthy, 1960 2 How did we get here? Security and Cloud Computing 3 What Is Cloud Computing? On-demand self-service Add or
“… computation may someday be organized as a public utility…” – John McCarthy, 1960
Security and Cloud Computing 2
How did we get here?
Security and Cloud Computing 3
- On-demand self-service
- Add or subtract resources as necessary
- Broad network access
- Mobile, desktop, mainframe
- Resource pooling
- Multiple tenants share resources that can be reassigned
dynamically according to need and invisibly to the tenants
- Rapid elasticity
- Services can quickly and automatically scale up or down to meet
customer need
- Measure service
- Like water, gas, or telephone service, usage can be monitored for
billing
What Is Cloud Computing?
4
Security and Cloud Computing
5
S E C U R I T Y
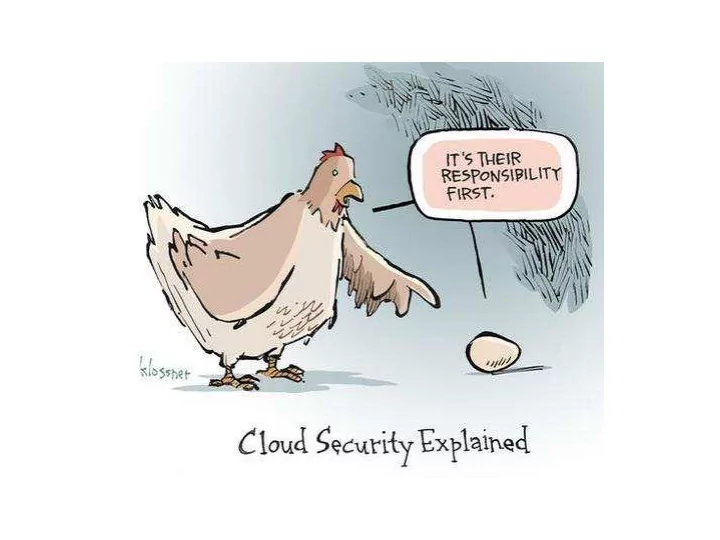
Cloud Model Applies at all Levels of the IT Stack – Resulting in Different Security Requirements, Different Responsibilities
Curtain
S E C U R I T Y S E C U R I T Y
The Cloud Curtain The Cloud Curtain 5
Service Models
Hardware: Servers, Storage Devices, and Networking Equipment Hypervisor Virtual Machines, Virtual Volume Storage, Virtual Networking Equipment Application Platform: Tools and APIs for Building and Deploying Applications Applications Administered by the SaaS Provider Administered by the PaaS Provider Administered by the IaaS Provider
6
Security and Cloud Computing
Customization, efficiency, availability, resiliency, security and privacy … Standardization, capital preservation, flexibility and time to deploy …
Public …
- Access open to everybody,
subject to subscription
- Shared resources
- Multiple tenants
- Delivers select set of
standardized business process, application and/or infrastructure services on a flexible price per use basis
- Always managed and hosted
by 3rd party
Private …
- Access limited to enterprise
and its partner network
- Dedicated resources
- Single tenant
- Drives efficiency,
standardization and best practices while retaining greater customization and control
- Might be managed or hosted
by third party
Cloud Computing Model Cloud Services
Cloud Computing Delivery Models
Hybrid …
- Private infrastructure,
integrated with public cloud
Community …
- Several organizations with
similar needs and policies share a private cloud
7
Move it to the cloud?
8
Security and Cloud Computing
Compliance
Complying with SOX, HIPAA and other regulations may prohibit the use
- f clouds for some applications.
Control
Many companies and governments are uncomfortable with the idea of their information located on systems they do not control.
Security Management
Even the simplest of tasks may be behind layers of abstraction or performed by someone else.
Data
Migrating workloads to a shared network and compute infrastructure increases the potential for unauthorized exposure.
Categories of Cloud Computing Risks
Providers must offer a high degree of security transparency to help put customers at ease. Authentication and access technologies become increasingly important. Mission critical applications may not run in the cloud without strong availability guarantees. Comprehensive auditing capabilities are essential. Providers must supply easy controls to manage security settings for application and runtime environments.
Reliability
High availability will be a key concern. IT departments will worry about a loss of service should outages occur.
9
Cloud Migration Risk Analysis
- Identify assets
- Determine vulnerabilities
- Estimate likelihood of exploitation
- Compute expected loss
- Survey and select new controls
- Project savings
10
- How sensitive is the data moving to the cloud?
- Do we need to share that data with anyone? What
access controls are needed?
- Export controls or other regulations?
- Does the CSP expect us to share our crypto keys with
them?
- How will the CSP support changing crypto keys?
11
Cloud Storage
- By default, most cloud storage solutions either store
users’ data unencrypted or encrypt all data for all customers using a single key and therefore don’t provide strong confidentiality
- Some cloud services provide better confidentiality by
generating keys on a per-user basis based on that user’s password or some other secret
- For maximum confidentiality, some cloud providers
embrace a trust no one (TNO) model in which even the provider does not have the keys to decrypt user data
12
Cloud Provider Assessment
- Security issues to consider:
- Authentication, authorization, and access control options
- Encryption options
- Audit logging capabilities
- Incident response capabilities
- Reliability and uptime
- Resources to help with assessment:
- FedRAMP
- PCI DSS
- CSA STAR
13
Switching Cloud Providers
- Switching cloud providers is expensive and difficult but
sometimes becomes necessary and urgent
- It is best to have backup options in place in case a
migration away from a cloud provider is necessary, but many cloud providers make that practically impossible
- SaaS providers are generally hardest to migrate away
from, followed by PaaS, then IaaS
14
What about security in the cloud?
Security and Cloud Computing 15
Security Benefits of Cloud Services
- Geographic diversity
- Many cloud providers run data centers in disparate geographic
locations and mirror data across locations, providing protection from natural and other local disasters.
- Platform and infrastructure diversity
- Different platforms and infrastructures mean different bugs and
vulnerabilities, which makes a single attack or error less likely to bring a system down. Using cloud services as part of a larger system can be a good way to diversify your technology stack.
16
Cloud-Based Security Functions
- Some security functions may be best handled by cloud
service providers:
- Email filtering
- Since email is already hopping through a variety of SMTP servers,
adding a cloud-based email filter is as simple as adding another hop.
- DDoS protection
- Cloud-based DDoS protection services update your DNS records to
insert their servers as proxies in front of yours. They maintain sufficient bandwidth to handle the flood of attack traffic.
- Network monitoring
- Cloud-based solutions can help customers deal with steep hardware
requirements and can provide monitoring and incident response expertise.
17
What about data protection in the cloud?
Security and Cloud Computing 18
Cloud Functionality vs. Privacy
If we have to choose, which do you think will win?
Security and Cloud Computing 19
–Trevor Pott (The Register)
“The old way is to treat our infrastructure as pets: you name your equipment and when it gets sick you nurse it back to health. The new way is to treat your infrastructure as cattle: you number your equipment and when one gets sick you shoot it.”
20
Homomorphic Encryption
21
Illustration from American Scientist, 2012
22
Illustration from American Scientist, 2012
23
Illustration from American Scientist, 2012
24
Illustration from American Scientist, 2012
25
Performance then and now
- Prior to Gentry’s breakthrough, HE was essentially
impossible
- Over the last four years, performance has improved by 3
- rders of magnitude (3500x)
– 2010 : 2 gates in 1 hour – 2013 : 128-bit AES, 20000 gates, in 3 hours – 2018 :
26
IBM’s HElib* on github
HElib is a software library that implements homomorphic encryption (HE). This library is written in C++ and uses the NTL mathematical library. It is distributed under the terms of the GNU General Public License (GPL).
* https://github.com/shaih/HElib
27