Case-control studies and cybercrime
Tyler Moore
Computer Science & Engineering Department, SMU, Dallas, TX
Lecture 14
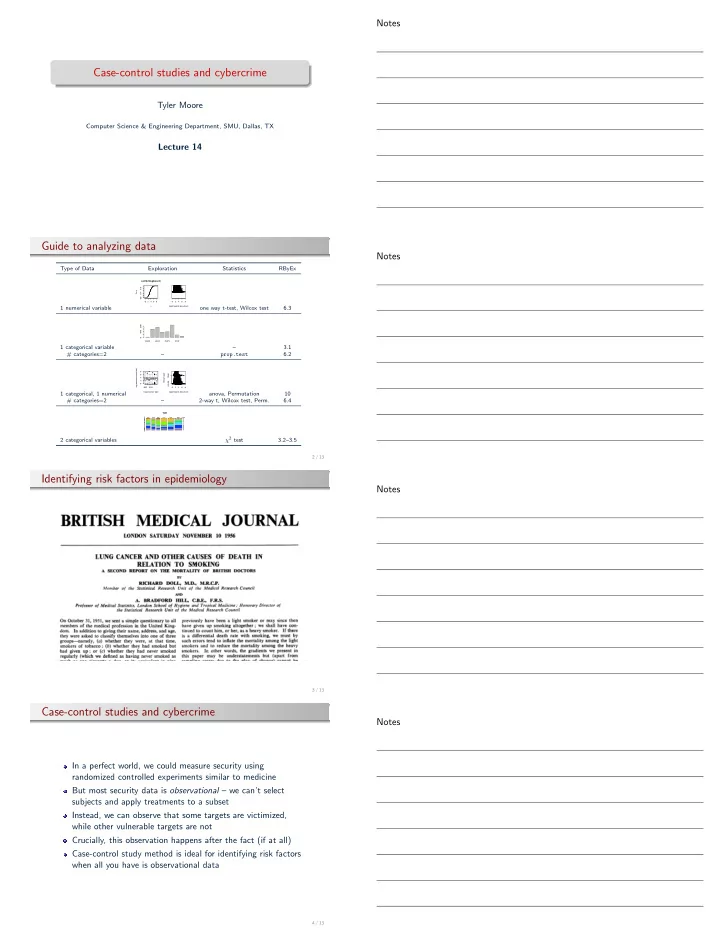
Guide to analyzing data
Type of Data Exploration Statistics RByEx 1 numerical variable
2 4 6 8 0.0 0.4 0.8 ecdf(br$logbreach) x Fn(x) 2 4 6 8 log(#records breached)
- ne way t-test, Wilcox test
6.3 1 categorical variable
CARD HACK PHYS STAT 400 800
– 3.1 # categories=2 – prop.test 6.2 1 categorical, 1 numerical
- BSF
EDU 2 4 6 8 Organization Type log(#records breached) 2 4 6 8 FALSE TRUE log(#records breached) Breach type
- ●
- anova, Permutation
10 # categories=2 – 2-way t, Wilcox test, Perm. 6.4 2 categorical variables
TOH
BSF BSO BSR EDU GOV MED NGO CARD DISC HACK INSD PHYS PORT STAT UNKN
χ2 test 3.2–3.5
2 / 13
Identifying risk factors in epidemiology
3 / 13
Case-control studies and cybercrime
In a perfect world, we could measure security using randomized controlled experiments similar to medicine But most security data is observational – we can’t select subjects and apply treatments to a subset Instead, we can observe that some targets are victimized, while other vulnerable targets are not Crucially, this observation happens after the fact (if at all) Case-control study method is ideal for identifying risk factors when all you have is observational data
4 / 13