1
1
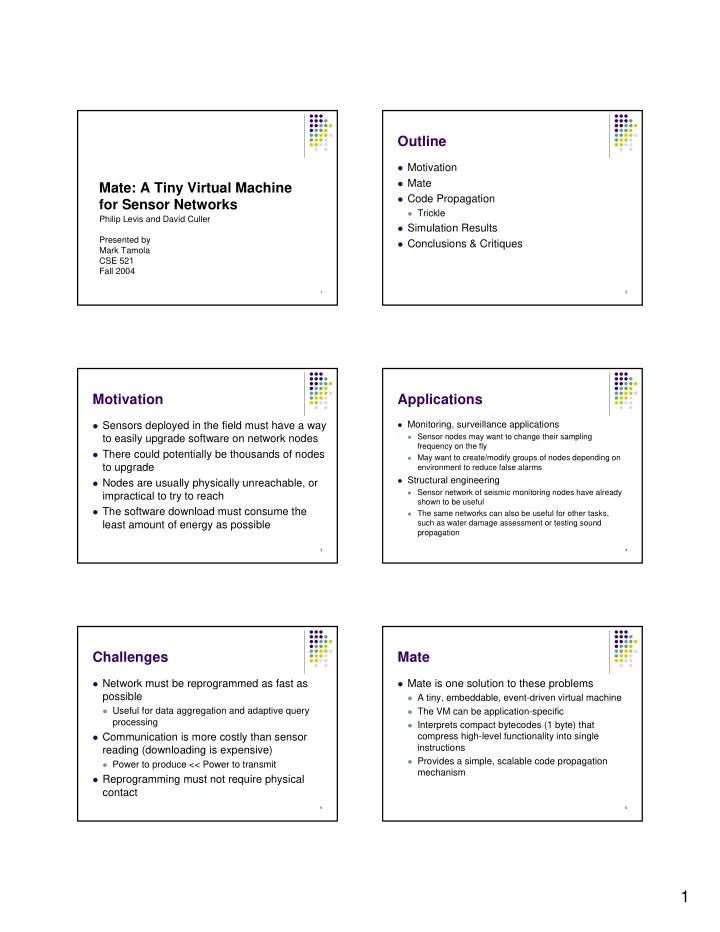
Mate: A Tiny Virtual Machine for Sensor Networks
Philip Levis and David Culler Presented by Mark Tamola CSE 521 Fall 2004
2
Outline
Motivation Mate Code Propagation
Trickle
Simulation Results Conclusions & Critiques
3
Motivation
Sensors deployed in the field must have a way
to easily upgrade software on network nodes
There could potentially be thousands of nodes
to upgrade
Nodes are usually physically unreachable, or
impractical to try to reach
The software download must consume the
least amount of energy as possible
4
Applications
Monitoring, surveillance applications
Sensor nodes may want to change their sampling
frequency on the fly
May want to create/modify groups of nodes depending on
environment to reduce false alarms
Structural engineering
Sensor network of seismic monitoring nodes have already
shown to be useful
The same networks can also be useful for other tasks,
such as water damage assessment or testing sound propagation
5
Challenges
Network must be reprogrammed as fast as
possible
Useful for data aggregation and adaptive query
processing
Communication is more costly than sensor
reading (downloading is expensive)
Power to produce << Power to transmit
Reprogramming must not require physical
contact
6
Mate
Mate is one solution to these problems
A tiny, embeddable, event-driven virtual machine The VM can be application-specific Interprets compact bytecodes (1 byte) that
compress high-level functionality into single instructions
Provides a simple, scalable code propagation